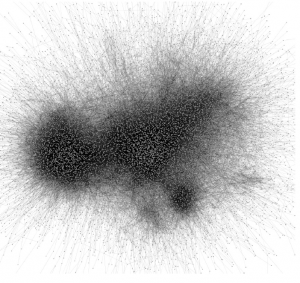
 Edward Snowden set off a maelstrom with his revelation concerning the covert use of phone records and possibly a greater range of information. For those of us in the Big Data technology universe, the technologies and algorithms involved are utterly prosaic: given the target of an investigation who is under scrutiny after court review, just query their known associates via a database of phone records. Slightly more interesting is to spread out in that connectivity network and identify associates of associates, or associates of associates who share common features. Still, it is a matching problem over small neighborhoods in large graphs, and that ain’t hard.
Edward Snowden set off a maelstrom with his revelation concerning the covert use of phone records and possibly a greater range of information. For those of us in the Big Data technology universe, the technologies and algorithms involved are utterly prosaic: given the target of an investigation who is under scrutiny after court review, just query their known associates via a database of phone records. Slightly more interesting is to spread out in that connectivity network and identify associates of associates, or associates of associates who share common features. Still, it is a matching problem over small neighborhoods in large graphs, and that ain’t hard.
The technological simplicity of the system is not really at issue, though, other than to note that just as information wants to be free—and technology makes that easier than ever—private information seems to be increasingly easy to acquire, distribute, and mine. But let’s consider a policy fix to at least one of the ethical dilemmas that is posed by what Snowden revealed. We might characterize this by saying that the large-scale, covert acquisition and mining of citizen data by the US government violates the Fourth Amendment. Specifically, going back in the jurisprudence a bit, when we expect privacy and when there is no probable cause to violate that privacy, then the acquisition of that information violates our rights under the Fourth. That is the common meme that is floating around concerning Snowden’s revelations, though it is at odds with widespread sentiment that we may need to give up some rights of privacy to help fight terrorism.
I’m not going to argue here about the correctness of these contending constructs, however. Nor will I address the issue of whether Snowden should have faced the music, fled, or whether he simply violated a rule and an oath requiring secrecy. Instead, I want to drill into one technical aspect of the way in which data was apparently acquired. The methodology that was employed (and more details may change this description) involved certification of the legality of the program by the Foreign Intelligence Surveillance Act (FISA) courts. The order from the court was closely held since it was all secret, of course, though there may have been a path for the telco providers to appeal to the FICA (Foreign Intelligence Court of Appeals) and possibly even to the Supreme Court under the terms of the Protect America Act of 2007. But why would the telcos bother unless it posed a risk of time, money, or peccant customer aggravation in some distant future?
So the point I am making is that there should be a path for judicial review that provides for an adversarial engagement with the Justice Department and the Intelligence Community. When Justice or Three-Letter Agency ABC wants to tap 50 million phones, they can approach the FISA court with their request. The court then provides the request to a cleared group of Constitutional lawyers who report to some Judicial Branch Office of Special Defense and are charged with representing the American people in these deliberations. I call them the FICLOs (Foreign Intelligence Court Loyal Opposition). These attorneys will be sworn to secrecy, as well, but will have an out in their secrecy clause that says that if they identify clear malfeasance in the process of FISA to FICA to SCOTUS escalation they are required to inform Congress (sure, initially in the Intelligence Committee). The end result injects a modicum more scrutiny into the process and perhaps saves us all from excessive overreach while providing a path for necessary secrecy.